This post originally appeared on AVNation.tv on Friday, October 13, 2015 as part of the AVNation’s 31 for 31 during October.
A jarring question but an important one. This question can be scary to think about at times but it needs to be addressed and thought about. For many in the AV industry the laptop is the tool of the trade. It is used to configure DSP engines, program control systems, and often calibrate the system. That is in addition to the key tasks it plays in business as being the e-mail, billing, and documentation tool.
Most people I have asked this question indicate that they have everything backed up to a USB thumbdrive. So then I ask the next important question, where is your USB thumbdrive? About half the time it is in their pocket the other time, it is in the laptop bag. So while that USB thumbdrive may help mitigate computer failures it does not address the loss of the laptop bag itself.
The part that most people miss is that-*when a laptop disappears a data breach just occurred. Let me repeat that, the data on the now missing laptop has most likely been breached. Typically people have lots of information on their laptop that they have not considered. The main ones to consider are passwords, account information and e-mails. Many people use the convenience feature of having a website “remember” their credentials. My first concern for the types of websites being accessed is of course the banking, travel, and shopping websites. That completely overlooks things such as possible network credentials for VPN that would let miscreants easily access to your company network.
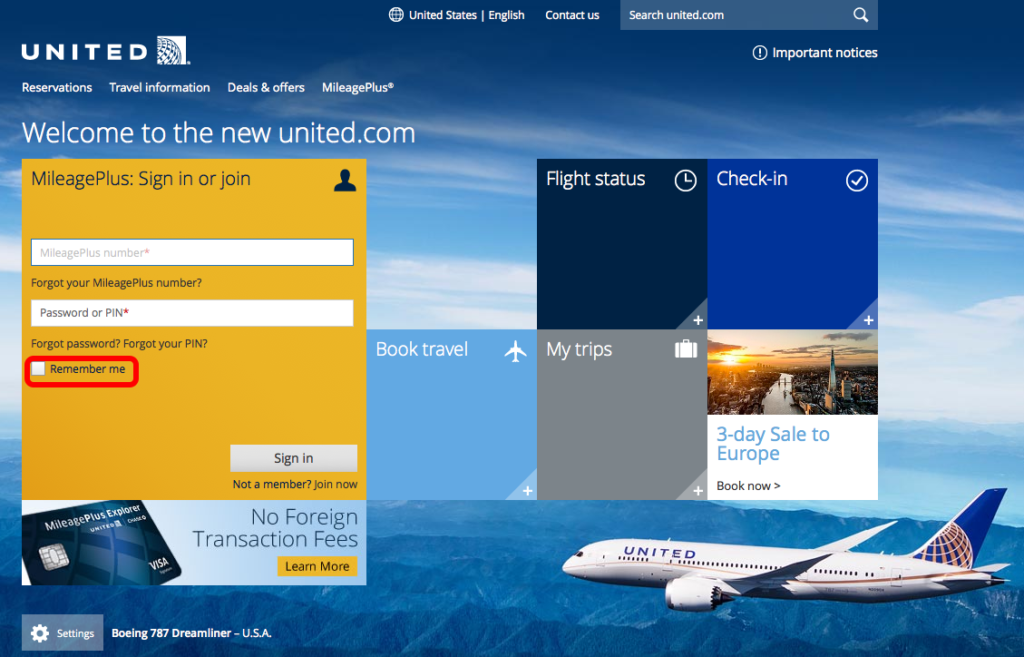
There are some relatively easy things that can be done to prevent this situation. The obvious one is to not lose your laptop bag. The next-*is to encrypt your hard drive. Encrypting your hard drive limits the ability to access-*your hard drive by a nefarious person. The second one is to not have your browser store your login passwords. Something I have found out is that after an upgrade of a browser, your preferences may get changed. This one is especially important if one follows the other alarming trend of using the same passwords in multiple places. Most of us have already thought about that step but then become complacent and frustrated by remembering all the passwords. Using a spreadsheet that contains all the passwords and account numbers is not-*the answer. A password manager will greatly help with this task and insure that you are using strong passwords. For various reasons I recommend against ones that store your passwords online. There are many available but comparing and contrasting them is for another blog post.
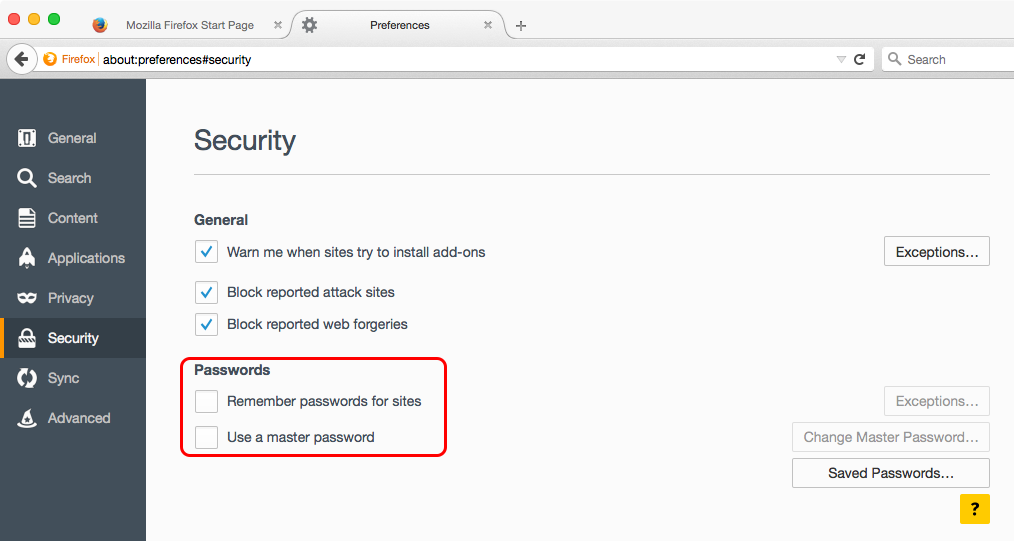
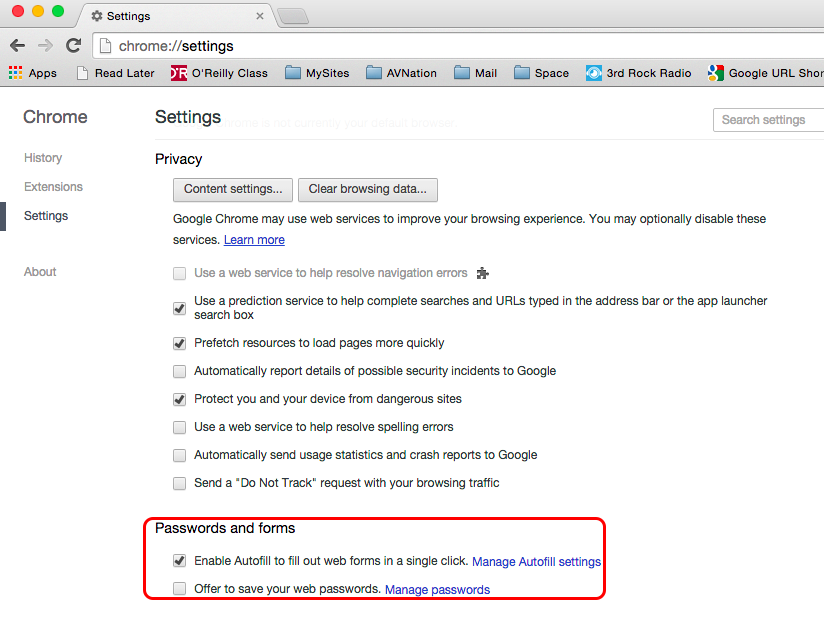
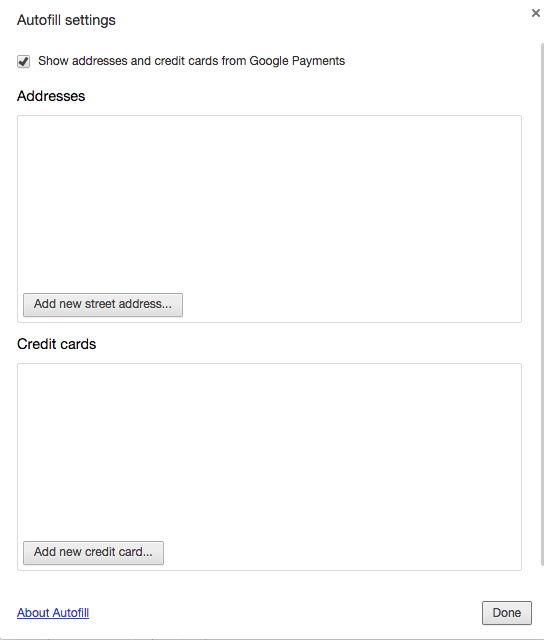
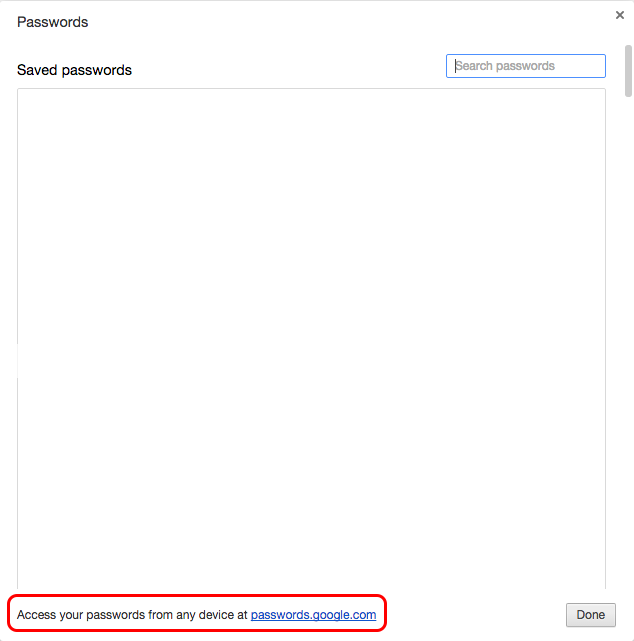
Another thing to be aware of is that Chrome saves your AutoFill information, which quite often includes your mailing address. Please consider whether or not you want to store and possibly share that information. Also, if you store a password in Google Chrome it is also stored on Google’s computers as well as available on the Internet at-*https://passwords.google.com.
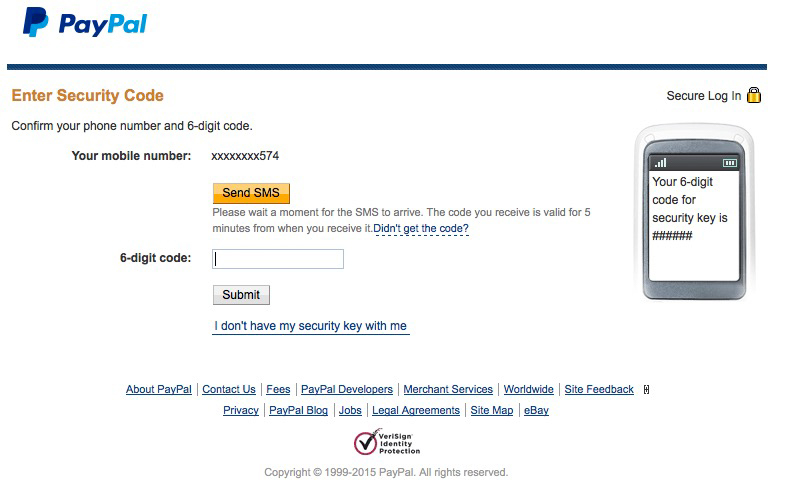
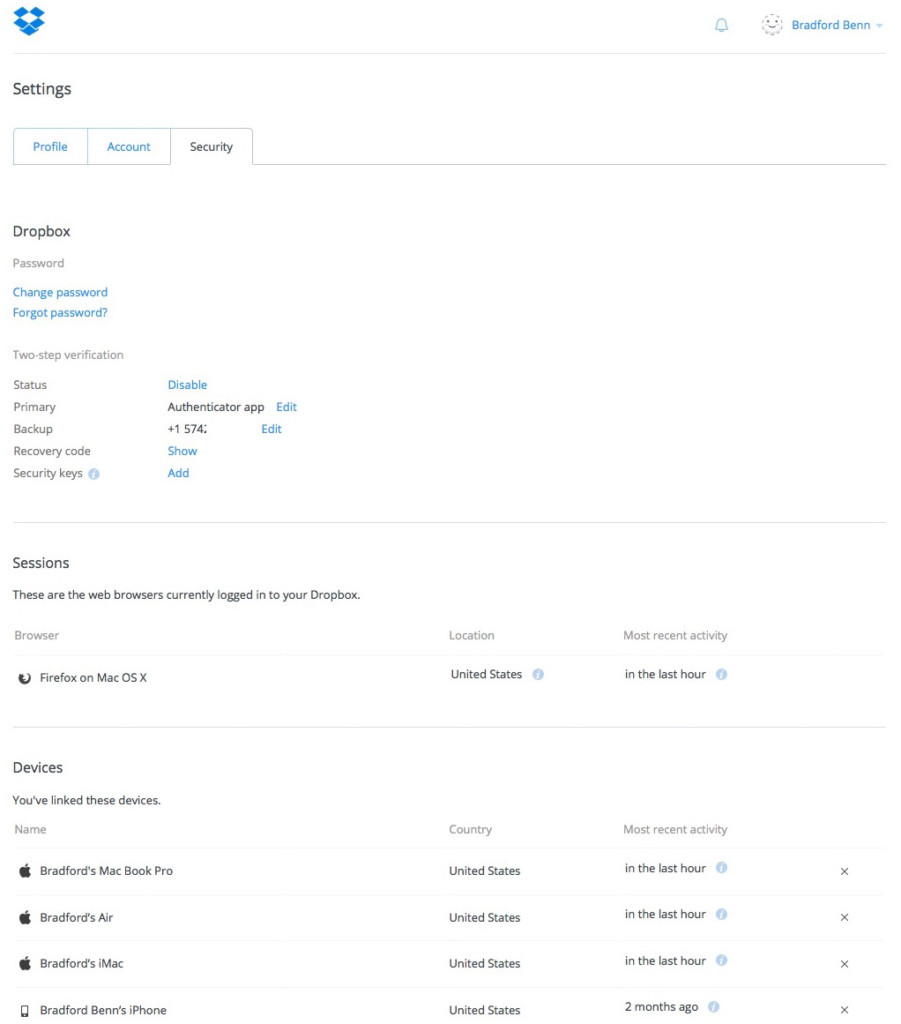
The option to me that is most effective is Two-Factor Authentication, often abbreviated as 2FA or TFA. Not every application supports this feature, and many of the ones that do are web based. This process requires two pieces of data in order to be able to complete a login, or authenticate into the system. The two most common ways to do this task are-*either using a token or having the service send you a message to confirm that you are making the request. Examples of these processes are PayPal sending a text message to a user that needs to be entered. The other typical case is using a token generator; an example of this approach is Dropbox if 2FA is enabled. The token generator can be installed on a device such as a smart phone, the generator then needs to be configured to work with the website.
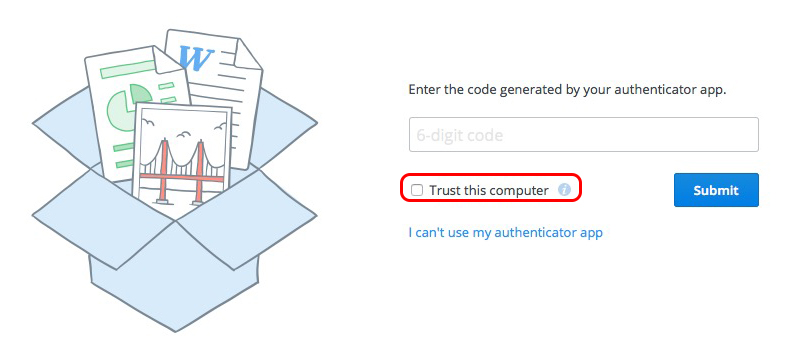
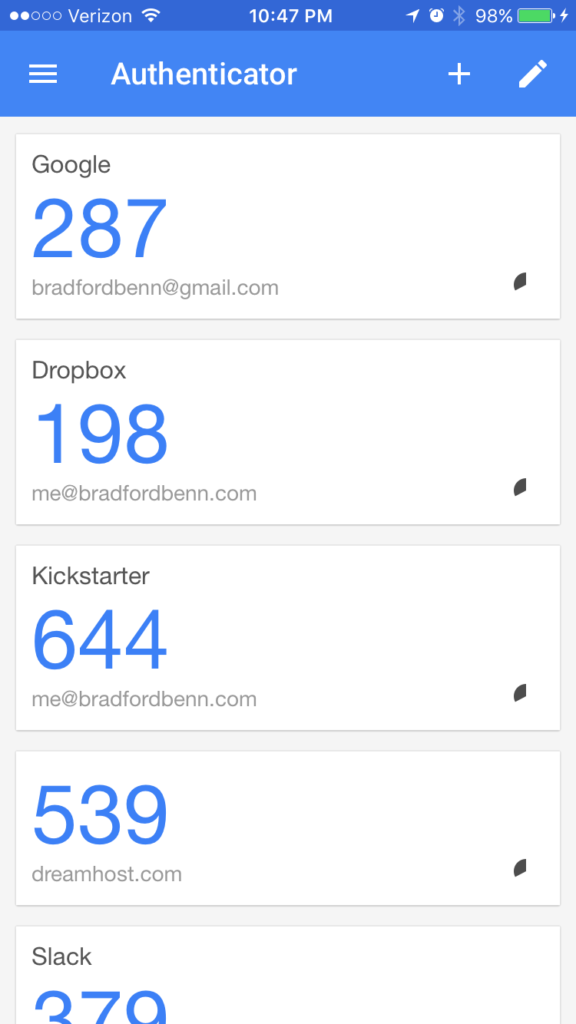
Two factor is a great tool to make impersonating you harder. This idea is also predicated on the idea that your token generator is not in your laptop case at the time of loss. Typically there is a weakness of allowing a computer to be remembered and validated as shown above. That setting basically turns off two-factor authorization on that computer.
An important thing to have is a way to deauthorize your computers. The same way one would call the credit card company to turn off a credit card that has been lost, one needs to do that for the missing laptop as well. To complete this task one typically needs another computer and the credentials to be able to login and deauthrorize the accounts in question. Most applications will also allow you to see the last time that device was connected to the service.
I hope this helps you. Make sure to check with your company’s IT department to see if they have plans in place for a lost device. Remember, security is a process not a destination. It takes constant attention to remain safer.
1 thought on “A Horror Story: Are you ready to lose your laptop bag?”
Comments are closed.